Assignment
No. 01
Semester Fall 2011
Database Management Systems-CS403
GOOD LUCK
Semester Fall 2011
Database Management Systems-CS403
Total Marks: 20
|
Due Date: 01/11/2011
Objective:
To learn and understand the
basic concepts of Context Level DFD and Cross Reference Matrix.
Instructions:
Please read the following instructions carefully before
solving & submitting assignment:
It
should be clear that your assignment will not get any credit if:
o
The assignment is
submitted after due date.
o
The submitted assignment
does not open or file is corrupt.
o
The assignment is copied
(from other student or copy from handouts).
o
The assignment is in the
format other than MS Word (doc).
o
Student ID is not
mentioned in the assignment File or name of file is other than student ID.
For any query
about the assignment, contact at cs403@vu.edu.pk
|
Q
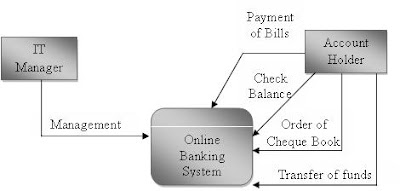
# 1: Draw a Context Level DFD for “Online Banking System” of ABC Bank. (10 marks)
Scenario
is given below:
Account Holder and IT Manager interact with
the system:
·
Account Holder perform following activities:
a. He can check his balance.
b. He can order a “Cheque Book”.
c. He can transfer funds from
one account to another account.
d. He can pay utility bills.
|
·
IT Manager manages the “Online Banking System”.
Q # 2: Analyze and Draw a “Cross Reference Matrix” to
identify/show different reports and attributes, which are usually required by
the higher management of ABC Bank (Any Bank). (10
marks)
Note: There should be 3 reports and 7 attributes in
the matrix.
|
|
Profit
& Loss Report
|
Final
Report
|
Expanse Report
|
Report
About Loans taken
|
|
Income
tax
|
√
|
√
|
|
|
|
Fixed
Assets
|
√
|
√
|
√
|
√
|
|
Income
|
√
|
√
|
|
|
|
Loss
|
√
|
√
|
|
|
|
Expanses
|
√
|
√
|
√
|
|
|
Name
of the company
|
|
|
|
√
|
|
Interest
|
√
|
√
|
√
|
√
|
|
Date
|
√
|
√
|
√
|
√
|